Agent Hooks
Table of Contents
Abstract
Agent Hooks is an open specification for structured lifecycle events emitted by AI-powered developer tools, agents, and assistants. It defines a vendor-neutral format for recording what an AI agent did, who initiated it, and why enabling cost transparency, security auditing, policy enforcement, and agent observability across any compliant tool.
1. Motivation
Modern AI coding tools such as Cursor, Windsurf Cascade, Claude Code, Google Gemini CLI, GitHub Copilot, and Codex operate as stateful agents, not stateless APIs. Each tool has independently introduced "hook" event systems that let developers intercept agent actions at key lifecycle points. The capabilities converge, but the naming, schemas, and feature sets diverge:
Cursor:
beforeShellExecution,afterFileEdit,afterAgentResponseClaude Code:
PreToolUse,PostToolUse,SessionStart,PreCompactWindsurf Cascade:
PreRunCommand,PostWriteCode,PreMCPToolUseGemini CLI:
BeforeTool,AfterAgent,PreCompressGitHub Copilot:
preToolUse,postToolUse,sessionStart
As a result:
Users cannot compare cost or execution behavior across tools
Platform vendors lack a shared accountability format
Third-party tooling (cost, security, compliance) requires custom integration per vendor
Token consumption are opaque or delayed
No shared vocabulary exists for "what just happened"
Agent Hooks defines a minimal but extensible event surface for AI-native workflows, providing the common language that is missing.
2. Goals
Interoperability: Any compliant tool can emit and consume hook events in one format.
Granularity: Support events from session lifecycle through individual tool invocations.
Attribution: Every event carries identity (who), action (what), and rationale (why).
Extensibility: Vendors can add custom metadata without breaking compatibility.
Human & Machine Readable: Events are JSON and readable without special tooling.
3. Non-Goals
Standardizing Prompts: Agent Hooks does not define prompt formats or agent logic.
Replacing Internal Telemetry: Vendors may keep their own systems; Agent Hooks is the external contract.
Prescribing Behavior: The spec standardizes signals, not how agents should act.
Transport Protocol: Delivery mechanism (stdout, HTTP, gRPC, queues) is out of scope.
UI Requirements: Agent Hooks does not require any specific interface.
4. Terminology
Term
Definition
Hook Event
A single immutable fact emitted by an AI agent during its lifecycle
Actor
The entity initiating or executing an action (human, AI agent, or system)
Session
A bounded interaction window (IDE open→close, CLI invocation, agent run)
Action
An external operation performed by the agent (shell, file I/O, tool call)
Mode
The agent mode the hook event was in when emitted
Model
The AI model used when a hook event was emitted
Compaction
Summarization or removal of conversation history to fit context limits
Actor Types
Type
Code
Description
Hook Event
user
A single immutable fact emitted by an AI agent during its lifecycle
AI Agent
agent
The AI assistant or coding agent
System
system
Platform infrastructure (e.g., auto-compaction, timeout)
Agent Modes
Mode
Description
agent
Autonomous multi-step execution
plan
Planning or strategy sub-agent
execute
Code-writing execution phase
chat
Conversational interaction
edit
Direct file editing context
5. Architecture Overview
Agent Hooks is a data specification, not a product. It defines how to record hook events. Storage and transport mechanisms are implementation-defined.
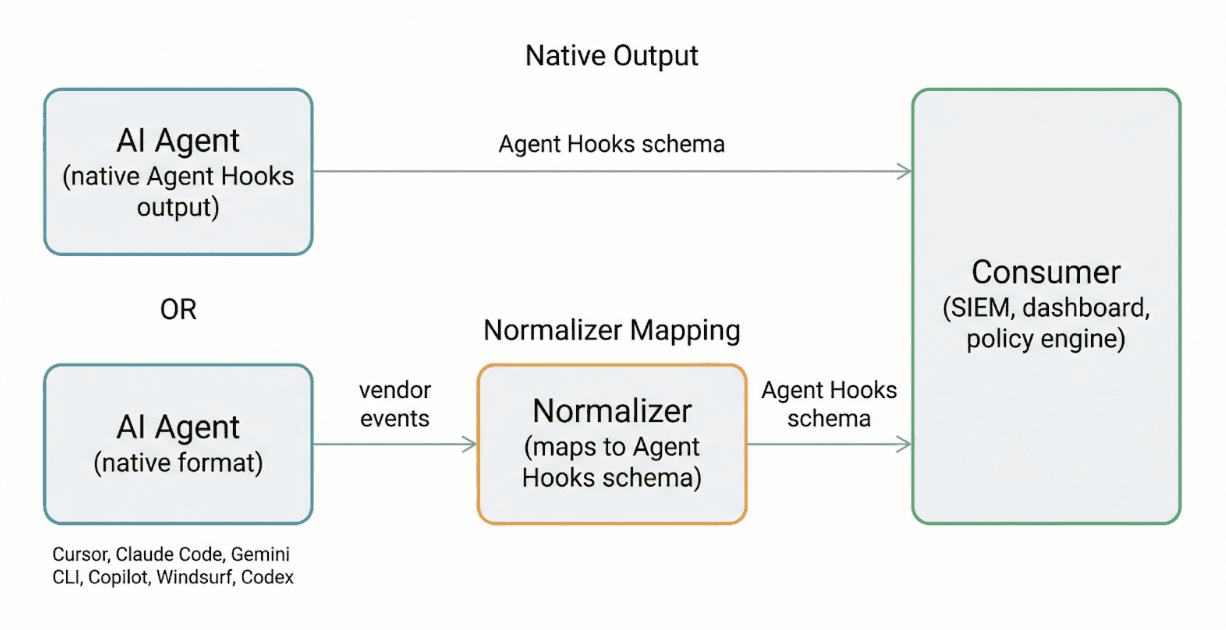
Each vendor maps its native events to the Agent Hooks schema. Consumers receive a unified stream regardless of which tool emitted the event.
6. Core Specification
6.1 Event Envelope Schema
Every hook event MUST include the following envelope:
6.2 Minimal Valid Event
6.3 Event Naming Convention
Event types use a dot-separated Category.Subcategory format. This avoids the fragmentation where beforeShellExecution (Cursor), PreRunCommand (Windsurf), preToolUse (Copilot), PreToolUse (Claude), and BeforeTool (Gemini) all describe the same concept.
Pattern
Meaning
Session.*
Session lifecycle
Prompt.*
User input events
Agent.*
Agent reasoning, planning, responses
Action.*
Tool/command execution
Model.*
LLM inference calls
Context.*
Context management (compaction)
Retry.*
Retry and loop detection
Policy.*
Safety and policy enforcement
7. Event Taxonomy
7.1 Session Lifecycle
Event Type
Description
Session.Start
New AI interaction begins
Session.End
Session ends normally
Session.Abort
Session terminated unexpectedly
Session.Start fields:
Session.End fields:
7.2 User Input
Event Type
Description
Prompt.Submitted
User submits a prompt or task
data SHOULD contain sanitized content. Raw prompt text is OPTIONAL and subject to the implementation's privacy policy.
7.3 Agent Reasoning & Planning
Event Type
Description
Agent.Plan.Start
Agent begins multi-step planning
Agent.Plan.End
Planning phase completes
Agent.Decision
Branching or selection made
Agent.Response
Agent produces final answer for the turn
data SHOULD contain summaries, not raw chain-of-thought.
7.4 Model Invocation
Event Type
Description
Model.Requested
LLM call initiated
Model.Responded
LLM response received
Model.Failed
LLM error
7.5 Action Execution
Event Type
Description
Action.Before
Tool/command execution about to begin
Action.After
Tool/command execution completed
These are the most critical events for security gating and observability.
Action.Before with decision:
Action.After with result:
Standard action names:
Action Name
Description
shell
Shell command execution
read_file
File read operation
write_file
File write or edit
mcp:<tool>
MCP tool invocation
web_search
Web search or fetch
code_edit
Inline code modification
7.6 Context Management
Event Type
Description
Context.UntilCompaction
Reports current context usage as a percentage of the compaction threshold
Context.Compaction
Context about to be compacted/summarized
Context.UntilCompaction tracks how close a session is to triggering compaction. Implementations SHOULD emit this event periodically or after each model invocation so consumers can monitor context pressure and anticipate compaction.
Context.Compaction fires when compaction is about to occur:
7.7 Notifications & Errors
Event Type
Description
Agent.Notification
Agent issues a notification or permission prompt
Agent.Error
Unexpected error in the agent loop
8. Vendor Alignment
The following table maps each vendor's native event names to the unified Agent Hooks types:
Agent Hooks Event
Cursor
Windsurf Cascade
Claude Code
Gemini CLI
GitHub Copilot
Session.Start
(implicit)
(on worktree setup)
SessionStart
SessionStart
SessionStart
Session.End
stop
(implicit)
SessionEnd
SessionEnd
SessionEnd
Prompt.Submitted
beforeSubmitPrompt
PreUserPrompt
UserPromptSubmit
(via BeforeAgent)
userPromptSubmitted
Agent.Plan.Start
(n/a)
(n/a)
SubagentStart
(Plan)
BeforeAgent
(n/a)
Agent.Response
afterAgentResponse
PostCascadeResponse
Stop
AfterAgent
(implicit)
Model.Requested
(n/a)
(n/a)
(n/a)
BeforeModel
(n/a)
Model.Responded
afterAgentThought
(n/a)
(n/a)
AfterModel
(n/a)
Action.Before
beforeShellExecution, beforeReadFile, beforeMCPExecution
PreRunCommand, PreReadCode, PreWriteCode, PreMCPToolUse
PreToolUse
BeforeTool
preToolUse
Action.After
afterShellExecution, afterFileEdit, afterMCPExecution
PostRunCommand, PostWriteCode, PostReadCode
PostToolUse, PostToolUseFailure
AfterTool
postToolUse
Context.UntilCompaction
(none)
(none)
(none)
(none)
(none)
Context.Compaction
(none)
(none)
PreCompact
PreCompress
(none)
Agent.Notification
(none)
(none)
Notification, PermissionRequest
Notification
(none)
Agent.Error
(none)
(none)
PostToolUseFailure
(none)
errorOccurred
(n/a) indicates the vendor does not expose a discrete event for this concept. The behavior may be implicit or combined with another event.
9. Security Considerations
Events SHOULD be cryptographically signed if transmitted externally.
Raw prompt content SHOULD be redacted or hashed. The
prompt_hashis preferred overpprompt_text.PII MUST NOT be included by default. User identity fields should use organizational identifiers, not personal data, where possible.
Tool outputs MAY be summarized or truncated. Full stdout/stderr SHOULD NOT be included unless the consumer opts in.
Event transport SHOULD use TLS when transmitted over a network.
Implementations SHOULD provide a means to capture all events without enumerating each hook type (e.g.,
AGENT_HOOKS_LOG=<filepath>orevent: "*"wildcard configuration).
10. Extensibility
10.1 Specification Versioning
prompt_hashfollows semver.Minor version: additive changes (new optional fields, new event types).
Major version: breaking changes to required fields.
Event types are additive; new types do not require a version bump.
10.2 Vendor Metadata
Vendors MAY add custom fields under themetadata object using reverse-domain notation to avoid key collisions:
10.3 Vendor Metadata
Tools MAY emit event types beyond the core taxonomy. Custom types SHOULD use a vendor prefix:
vendor.cursor.TabFileEdit
vendor.gemini.ModelStream
Consumers MUST ignore unknown event types or fields.
10.4 Wildcard Hook Enablement
Implementations SHOULD provide a mechanism to capture all events in a single configuration statement. This ensures ease of adoption such so a security engineer can enable full telemetry in one step:
tool-native configuration:
11. Relationship to Existing Standards
Standard
Relationship
Agent Trace
Complementary. Agent Trace attributes code lines to AI or human contributors. Agent Hooks records the events and decisions that produced those contributions. A trace_record_idfield MAY link an Agent Hooks event to an Agent Trace record.
CloudEvents
Inspiration for the transport-neutral envelope structure. Agent Hooks events can be wrapped in CloudEvents for delivery.
MCP (Model Context Protocol)
Complementary. MCP describes agent capabilities and tool interfaces. Agent Hooks describes the events emitted when those capabilities are exercised.
12. Reference Implementation
A reference implementation demonstrating Agent Hooks integration with multiple AI coding tools is maintained in the Intentra CLI. The implementation includes:
Event normalizers for Cursor, Claude Code, Gemini CLI, Copilot, and Windsurf Cascade
Hook event handlers that map native events to the Agent Hooks schema
Scan aggregation that groups events into prompt-response cycles
Risk scoring based on the baseline guidelines in this spec
The reference normalizer interface:
Each tool's normalizer registers itself and maps native event names to Agent Hooks types. The normalized events are then forwarded to consumers (logging, dashboards, policy engines) in the unified JSON format.
13. Appendix
A. Complete Event Type Reference
Event Type
Category
Advisory Only
Description
Session.Start
Lifecycle
Yes
Session initiated
Session.End
Lifecycle
Yes
Session terminated
Session.Abort
Lifecycle
Yes
Session terminated unexpectedly
Prompt.Submitted
Input
No (can deny)
User submits prompt
Agent.Plan.Start
Reasoning
Yes
Planning phase begins
Agent.Plan.End
Reasoning
Yes
Planning phase completes
Agent.Decision
Reasoning
Yes
Agent makes a branching decision
Agent.Response
Reasoning
Yes
Agent produces final turn answer
Model.Requested
Model
Yes
LLM call initiated
Model.Responded
Model
Yes
LLM response received
Model.Failed
Model
Yes
LLM error occurred
Action.Before
Execution
No (can deny)
Tool/command about to execute
Action.After
Execution
Yes
Tool/command completed
Retry.Triggered
Retry
Yes
Retry initiated
Retry.Loop.Detected
Retry
Yes
Probable retry loop
Retry.Loop.Aborted
Retry
Yes
Loop forcibly stopped
Context.UntilCompaction
Context
Yes
Current context usage percentage
Context.Compaction
Context
Yes
Context about to be compacted
Policy.Violation
Safety
Yes
Policy breach detected
Policy.Blocked
Safety
Yes
Action prevented
Policy.Override
Safety
Yes
Human override granted
Agent.Notification
System
Yes
Notification or permission prompt
Agent.Error
System
Yes
Unexpected error
B. Full Example: Action Blocked
C. Full Example: Successful Shell Command
D. Full Example: Context Until Compaction
E. Full Example: Context Compaction
F. Full Example: Retry Loop Detected
G. MIME Type
Type
MIME Type
Hook Event
application/vnd.agent-hooks.event+json
Event Stream
application/vnd.agent-hooks.stream+jsonl
H. Delivery Mechanisms
Agent Hooks events MAY be delivered via any of:
Local stdout / file (JSONL format)
HTTP webhooks (POST per event or batched)
gRPC streams
OpenTelemetry exporters
Message queues (Kafka, SQS, etc.)
Transport selection is out of scope for this specification.
I. Open Questions
J. FAQ
How does Agent Hooks relate to Agent Trace?
Agent Trace records which lines of code were written by AI. Agent Hooks records the events and decisions that produced those lines. Together they provide end-to-end attribution: Agent Trace shows the "what was written" and Agent Hooks shows the "how and why it was written."
Do vendors need to change their internal hook systems?
No. Agent Hooks is an output format specification. Vendors map their native events to the schema at the point of export. Internal systems remain unchanged.
How should I store the events?
This spec intentionally does not define storage. Events can be written to local files, streamed to cloud logging, stored in databases, or forwarded to SIEMs.
Can I add custom events?
Yes. Use vendor-prefixed event types (e.g., vendor.cursor.TabFileEdit). Consumers MUST ignore unknown event types.
What about privacy?
Raw prompts and tool outputs are not required. Use hashes (prompt_hash, content_hash) and summaries by default. Full content inclusion is opt-in per implementation.
License
This specification is released under CC BY 4.0.
Contributing
This specification is accepting feedback and contributions. Early adopters are encouraged to implement read-only event emission first.
Want to join contributors? Email contact@atbabers.com with your LinkedIn Profile
Partners helping shape Agent Hooks:
Intentra
(Open for contributions from Cursor, Anthropic, Google, GitHub, Windsurf, and the broader community)
©2026 Asante Babers